Operational and Executive Exposure
Intelligence-led assessment of executive exposure, insider risk, and physical threat in complex environments.
Most security assessments are compliance-driven exercises that identify generic vulnerabilities without regard to actual threat. Veritas Intelligence evaluates risk differently - through a counterintelligence-informed approach that considers adversary capability, intent, and access.
Our work is informed by decades of real-world, high-stakes operational and corporate security experience. We identify where meaningful risk exists, how it is likely to develop, and what must be done to mitigate it.
Facility security, executive protection assessments, travel risk, and international operations security
Security assessments for offices, partner residences, high-profile litigation, and witness protection scenarios
Portfolio company security reviews, executive risk assessments, and due diligence on security posture
Residential security, personal threat assessments, travel security, and family protection planning
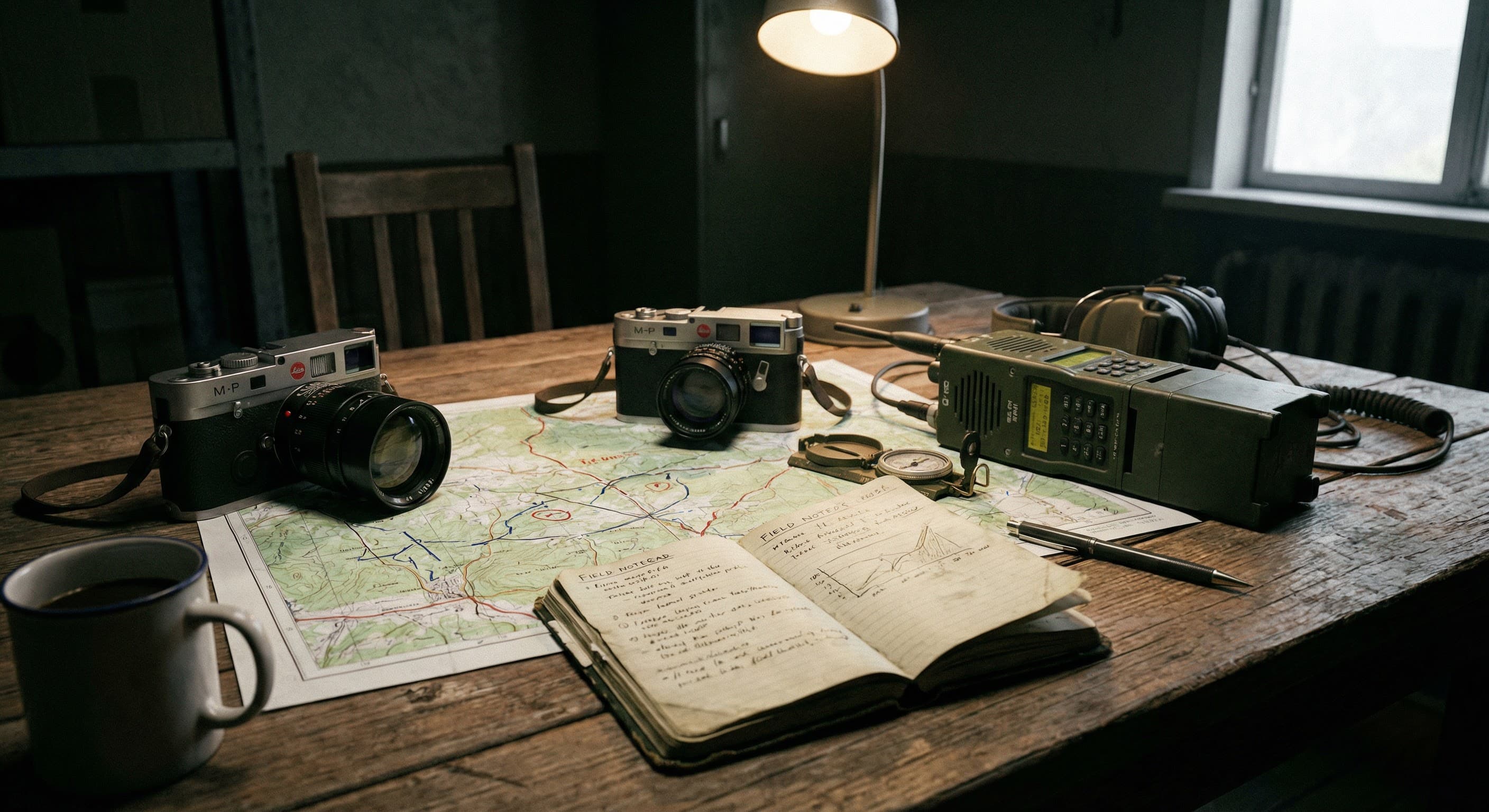
CIA Tradecraft Meets Corporate Security Leadership
Our founder spent decades conducting security operations at the highest levels of the U.S. intelligence community — including service as a CIA Senior Operations Officer and Chief of Station — before leading global safety and security for a Fortune 500 corporation. This dual perspective shapes every assessment.
- Retired CIA Senior Operations Officer, Directorate of Operations
- Fortune 500 Global Safety & Security executive
- Two-time Chief of Station in Latin America
- Senior instructor, CIA and DoD advanced training academies
- Former Special Agent, U.S. Army Counterintelligence
Security Consulting Services
Every engagement is tailored to the client's specific threat environment, asset profile, and operational requirements.
Physical Security Risk Assessments
Comprehensive evaluation of physical security posture for corporate facilities, executive residences, event venues, and critical infrastructure. Identifies vulnerabilities, assesses threat levels, and delivers prioritized recommendations — not generic checklists, but intelligence-informed assessments calibrated to actual risk.
Executive Security Risk Assessment
Threat and vulnerability assessment for senior executives, board members, and high-profile individuals. Evaluates personal security posture, travel risk, residential exposure, digital footprint, and the intersection of professional visibility with physical vulnerability.
Travel Risk & Route Security
Pre-travel intelligence and security planning for executives, legal teams, and corporate travelers operating in elevated-risk environments. Includes route analysis, secure transportation guidance, medical and evacuation contingency, and real-time monitoring during travel.
Threat Assessment & Management
Assessment of specific threats to personnel, operations, or assets — including workplace violence indicators, targeted threat actors, stalking and harassment patterns, and reputational threats that cross into physical risk. Structured methodology with actionable response recommendations.
International Security Consulting
Security consulting for organizations with international operations, expatriate personnel, or assets in complex jurisdictions. Covers political security risk, kidnap and extortion exposure, civil unrest preparedness, and facility security in regions where standard commercial security is insufficient.
Event & Venue Security
Security planning and risk assessment for corporate events, board meetings, shareholder gatherings, and private functions. Includes advance work, access control recommendations, protective intelligence, and coordination with venue and law enforcement resources.
Security Risk Management, Not Security Theater
Effective security risk management begins with understanding the actual threat — not the theoretical one. We assess who your adversaries are, what their capabilities look like, and where your specific vulnerabilities intersect with their intent. Then we deliver recommendations that are practical, proportionate, and implementable.
Identify actual adversary capability and intent — not theoretical risk from a generic matrix
Evaluate physical, procedural, and personnel vulnerabilities against the identified threat
Actionable mitigation measures ranked by impact and feasibility, not exhaustive checklists
Guidance through execution — vendor evaluation, policy development, and progress verification
Why Veritas Security Consulting Is Different
Intelligence-Led, Not Compliance-Driven
Our security assessments are informed by intelligence tradecraft — not checkbox compliance. We assess actual threat, not theoretical risk. Every recommendation is calibrated to the specific environment, adversary capability, and client risk tolerance.
Operational Experience at the Highest Levels
Our founder spent decades conducting security operations as a CIA Senior Operations Officer and subsequently served as a Fortune 500 Global Safety & Security executive. This combination of government intelligence and corporate security leadership is rare — and it shapes every engagement.
Discreet and Defensible
Security assessments are conducted with the discretion required for high-profile clients — executives, family principals, law firms, and organizations where public visibility of security concerns would itself create risk. Findings are documented to a standard suitable for legal and insurance review.
Engagement Process
Secure Intake & Scoping
Confidential consultation to understand the threat environment, asset profile, and specific security concerns. We define scope, timeline, and deliverables before beginning any assessment work.
Threat & Vulnerability Assessment
On-site and remote evaluation combining physical inspection, procedural review, personnel assessment, and intelligence analysis. We assess actual threat — not generic risk categories.
Analysis & Recommendations
Detailed findings with prioritized, actionable recommendations. Each recommendation is calibrated to the specific threat, ranked by impact and feasibility, and accompanied by implementation guidance.
Briefing & Implementation Support
Direct briefing to principals or designated security leadership. Ongoing advisory support available for implementation, vendor evaluation, and progress verification.

Require Security Consulting?
Contact Veritas Intelligence to discuss your security consulting requirements. All consultations are confidential and provided without obligation.
